WhatsApp has warned around 200 users after a fake version of its app was used to install government-grade spyware. WhatsApp has taken immediate steps to protect affected users, and the company will send a formal legal demand to stop any such malicious activity.
| Key Points | Details |
|---|---|
| Story about: | Fake WhatsApp app distributing government-grade spyware |
| Status: | Around 200 users notified |
| Affected versions: | Only unofficial, modified versions were affected. Official app remains safe. |
| Previous news: | How to use two-step verification to protect your WhatsApp account! |
WhatsApp alerts users after fake app used for government-grade spyware
WhatsApp has taken proactive action to protect its users after discovering a malicious fake version of the app. The unofficial application was secretly used to deploy government-grade spyware on iPhones. WhatsApp has notified around 200 users, primarily located in Italy, who were tricked into installing the malicious app. The fake iOS client was built by SIO, an Italian spyware manufacturer that develops surveillance tools for law enforcement and intelligence agencies.
What happened: a fake WhatsApp app hiding spyware
WhatsApp has identified approximately 200 users who may have downloaded a malicious version of the WhatsApp client on iOS. The unofficial app was not distributed through the App Store, but it was likely delivered through phishing links. A previous investigation by TechCrunch on other malicious Android apps connected to SIO identified the malware as "Spyrtacus". Once installed, the spyware can access private messages, contacts, microphone and camera data, and other sensitive information stored on the device. All without the user's knowledge or consent. Since these users installed the app from outside the official stores, they were exposed to serious security risks that could have been avoided by using the official WhatsApp app.
How WhatsApp responded
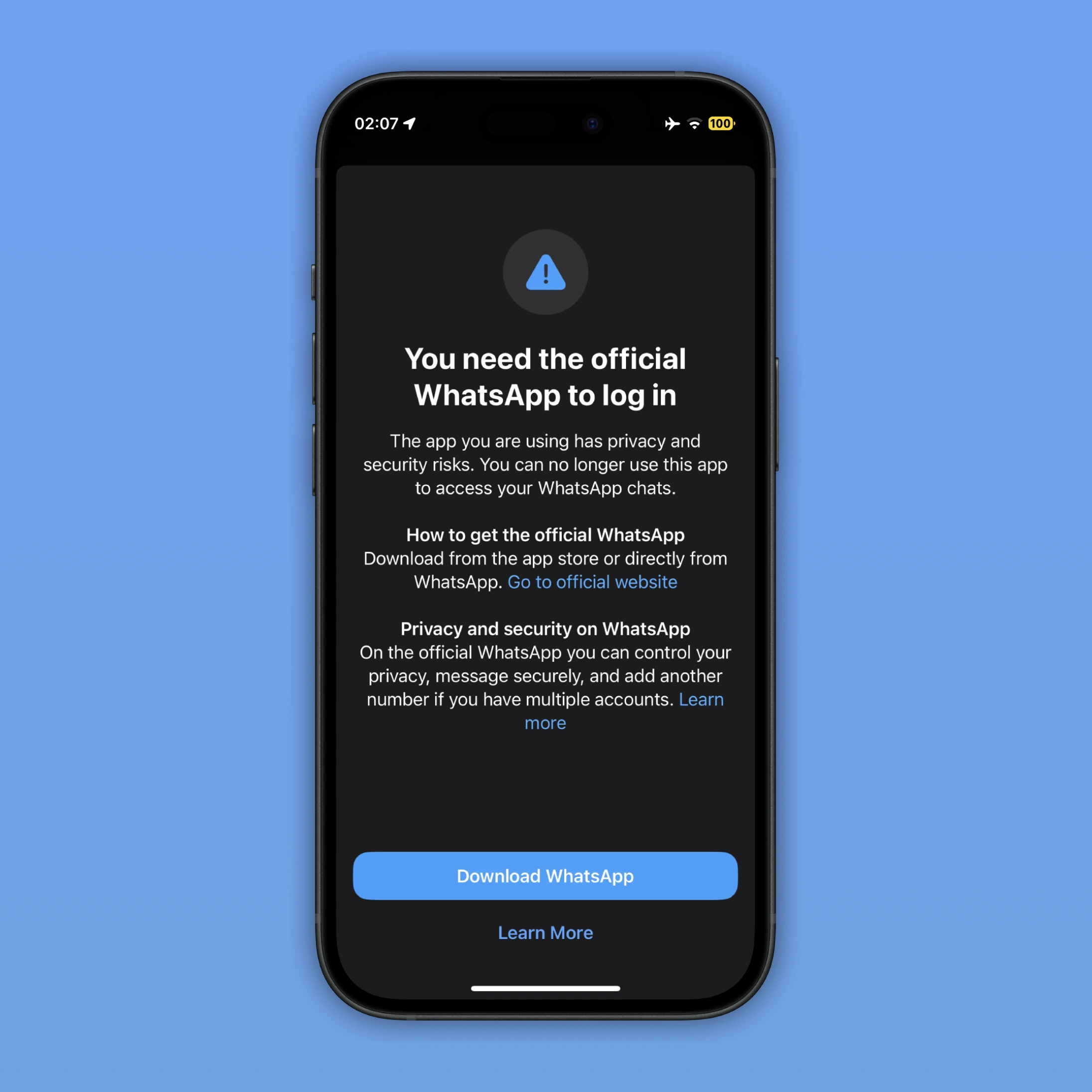
Once the spyware was identified, WhatsApp immediately informed affected users that they were using an unofficial app. WhatsApp has already logged out all identified users from the fake application, and the notification contained information about the privacy and security risks associated with downloading unofficial clients. In the same alert, WhatsApp strongly encouraged these users to remove the malicious app and reinstall the official WhatsApp version from the App Store.
WhatsApp spokesperson Margarita Franklin confirmed to TechCrunch that protecting affected users has been always a priority. However, she noted that further details about the identities or profiles of those notified (such as whether they include journalists or civil society members) could not be disclosed at this stage. WhatsApp has also announced to send a formal legal demand to SIO. This notice would require the Italian spyware maker to cease all such malicious activity.
A broader pattern: Italy's spyware problem
This is not the first time WhatsApp has been forced to act against state-sponsored spyware targeting its users, and Italy appears to be at the center of these recurring incidents. Just over a year ago, WhatsApp alerted approximately 90 users (including journalists and pro-immigration activists) that they had been targeted using spyware developed by Paragon Solutions, a US-Israeli surveillance technology company. That incident caused a significant scandal across Italy. Paragon subsequently cut ties with Italian spy agencies after it became clear that the spyware had been used against journalists and advocates.
The SIO case follows a remarkably similar pattern. Using fake apps as a vector for surveillance is a deeply entrenched tactic within Italian law enforcement. In a separate legal battle, WhatsApp and its parent company Meta sued the Israeli spyware maker NSO Group after it was found to have used the Pegasus tool to target more than 1400 users' devices with invasive spyware. That case ended in a major victory for WhatsApp, and a U.S. federal jury ordered NSO Group to pay around $167 million in damages. This ruling represents an important legal victory against the misuse of spyware.
What this means for WhatsApp users
It is important to note that these companies did not exploit any vulnerabilities. Users who downloaded and exclusively used the official WhatsApp application from the App Store, TestFlight, or Google Play Store were not at risk. The attack was entirely dependent on convincing targets to sideload or install an unofficial, modified version of the app. Attackers download WhatsApp, modify the app by adding spyware, and then make it available online. Then, they persuade users to download WhatsApp from another source by claiming that the app they are currently using has a security risk, even though the official app is actually secure. They may also promise additional features, such as tools to customize the app.
This incident reinforces a fundamental security principle that all users should keep in mind: always download apps exclusively from official stores. Additionally, users should be extremely cautious of links, particularly when they prompt them to install or update applications outside of the App Store. At the moment, it seems that WhatsApp has not confirmed whether the legal demand to SIO has been formally issued yet.
Stay Connected with WABetaInfo
Follow WABetaInfo on X to stay informed about new features and updates. We love hearing your feedback, so please let us know what you think! You can also visit our About page to explore all our services and keep up with the latest announcements.